Level 1: Getting Started Right
Gaining foundational certifications is a great first step to exploring cybersecurity roles. However, certifications alone are usually not enough. At this stage, hands-on practice matters. Choose certifications that include labs or simulations so you can apply what you learn in practical scenarios.
While a good certification helps you build foundational knowledge, you will also need to build proof of your skills alongside it. One effective way to do that is by practicing core analyst tasks on a daily basis. For instance, you can work with publicly available sample logs and try to identify suspicious IP addresses or unusual login patterns. Over time, this builds analytical skills relevant to your entry-level cybersecurity work.
Another important step is getting familiar with commonly used tools. Even at a beginner level, it is useful to explore security information and event management (SIEM) basics and endpoint security tools to understand how security teams monitor and investigate threats. It also helps to join cybersecurity communities and participate in real incident discussions so you can connect theory with common security issues in practice.
Level 2: Finding a Specialization
At this point in your career, you will recognize the work you prefer and the tasks you perform well. That self-awareness is important when choosing the right specialization. For example, if you enjoy analyzing alerts, threat detection may be a good fit, or if you prefer investigating incidents, incident response may be a better path.
Once you have this clarity, validate your choice before investing in a specialized certification. You can do this by taking on related tasks at work, shadowing experienced team members, and working through realistic case studies. This helps confirm whether your interests and skills align. After that, choose a certification based on the work you have done, what you have learned, and your long-term career direction.
Level 3: Advancing in Senior Technical or Team Leadership Roles
At this stage, professionals often deepen a specialization, take on broader ownership, or begin moving into team leadership. Depending on the organization, this can include roles such as senior analyst, threat hunter, incident response lead, security engineer, or early security management roles.
Instead of asking only, “What should I learn next?” ask, “What problem in my current role can I solve more effectively?” For example, you might reduce alert noise by identifying false positives and tuning detection rules, or improve response time by identifying workflow bottlenecks and tracking the results. As you do this, communicate the operational or business impact of those improvements, not only the technical changes.
Your approach to certifications should also change here. Rather than following trends, choose certifications that strengthen the knowledge domains most relevant to your role, such as incident handling, threat intelligence, forensics, cloud security, or leadership responsibilities.
Level 4: Executive Leadership and Strategic Management
Mapping EC-Council Certifications to Cyber Security Career Path
| Cyber Security Career Path | EC-Council Certifications | Core Learning Areas | Program Highlights |
|---|---|---|---|
| Ethical Hacking and Penetration Testing | CEH AI | Five phases of ethical hacking; AI-assisted ethical hacking; hacking tools and techniques; vulnerability identification and exploitation concepts; reporting and remediation | 221 hands-on labs; 4,000+ ethical hacking tools; 550+ attack techniques; AI-driven methods |
| CPENT AI | Advanced penetration testing; exploit development; advanced binary exploitation; hidden-network access; SCADA, cloud, OT, and IoT testing | 110+ advanced labs; live cyber ranges; 50+ tools; CTF challenges; AI techniques mapped to pen testing phases | |
| SOC and Threat Detection | CSA | SIEM deployment; SOC workflows; centralized log management; threat detection and investigation; incident triage and response; AI/ML capabilities for SOC | 50+ hands-on labs; 120+ tools; 65 widely applied SIEM use cases |
| CTIA | Threat-intelligence life cycle; threat data collection; threat analysis; intelligence production; intelligence sharing and integration | 200+ threat intelligence tools; 27 hands-on labs; 800+ pages of the comprehensive student manual; 40% lab-focused training | |
| ECIH | Incident-handling life cycle; incident analysis; containment and eradication; recovery and remediation; playbooks and documentation | 800+ incident handling and response tools; 125 incident handling templates, checklists, and toolkits; 95 labs simulating a real environment; 10+ incident handling playbooks and runbooks | |
| Network Defense | CND | Adaptive security approach; network security controls; risk management; security policies and solutions; incident response capabilities | 100+ hands-on labs; 50% lab-focused training; coverage of cloud, IoT, virtualization, remote worker threats, and attack surface analysis |
| Digital Forensics and Investigation | CHFI | Forensic readiness; forensics process; lab and evidence handling; incident validation and triage; investigation and reporting | Dark web and IoT forensics; 68 forensics labs; 600+ digital forensics tools; 70+ GB of evidence files for investigations; 40% lab-focused training |
| Cloud and DevSecOps Security | CCSE | Multi-cloud security; cloud security policies; identity and data protection; building, operating, and defending cloud environments; governance, risk, and compliance | Hands-on labs and real-world scenarios for AWS, Azure, and GCP; vendor-neutral training combined with vendor-specific instruction and performance labs |
| ECDE | Application and infrastructure security; security across the DevOps life cycle; DevSecOps tools and practices; secure development pipelines; cloud-native and on-premises security | 100+ labs; 70% lab-intensive training; 8 DevOps lifecycle stages; AI-powered tools | |
| Security Leadership and Governance | CCISO | Security governance and strategy; risk management; security operations oversight; leadership and executive decision-making; board, finance, procurement, and vendor management | 5 domains of executive security leadership; AI-enhanced governance and risk management; board-level communication and strategy; budget, finance, and vendor management |
Why Cybersecurity Skills Matter in 2026
A major reason organizations struggle with cyber resilience isn’t tools or budgets: it’s talent. Among organizations with insufficient levels of cyber resilience, 85% cited missing critical skills and people to fulfill cybersecurity objectives (World Economic Forum & Accenture, 2026).
While candidates with skills in network engineering and security experience remain difficult to find, those with cybersecurity and AI experience are fast becoming a close contender among the hardest to find, and modern technology roles in AI/machine learning and cloud security rank as the hardest to fill (Fortinet, 2025).
This creates opportunity for professionals who invest in building the right skills. EC-Council certifications are designed to help address these gaps.
EC-Council Certifications for Cybersecurity Careers in 2026
Designed around real-world job roles, EC-Council certifications cover a wide range of cybersecurity disciplines, offering specializations in ethical hacking, SOC operations, DevSecOps, threat intelligence, and more. These certifications are continually updated as the field of cybersecurity evolves, and flagship programs such as CEH AI, CPENT AI, and CCISO already include AI-focused content that reflects the emerging skill demands.
EC-Council also brings established global reach and training experience:
- 25+ years of cybersecurity training experience
- Presence across 170+ countries
- 400,000+ certified professionals worldwide
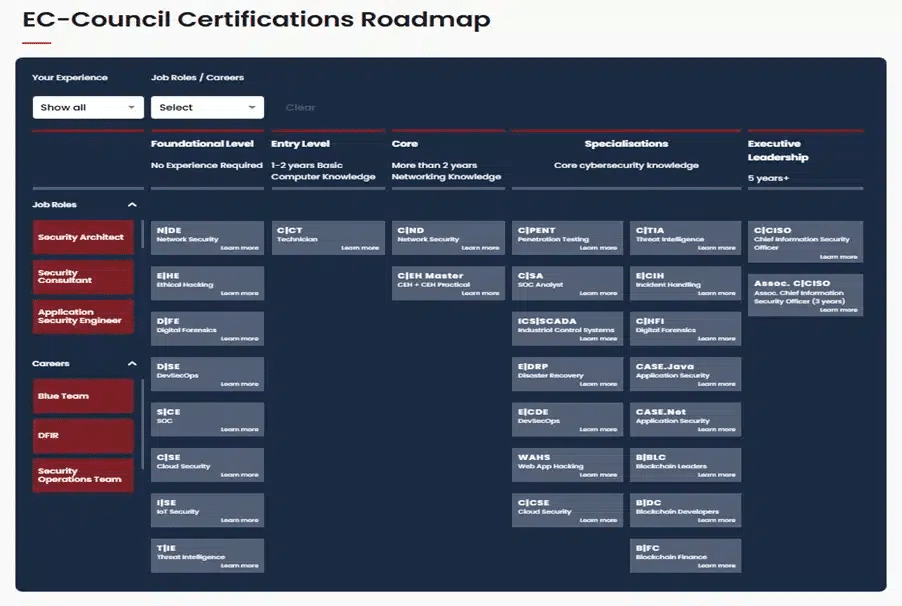
Now that you’ve explored a structured cybersecurity certification roadmap for 2026, the next step is to define your career path. Use the EC-Council cybersecurity certifications roadmap to identify the certification that best fits your current role and long-term direction.
FAQs
What is a roadmap for cybersecurity?
A cybersecurity roadmap is not just a list of topics or certifications to choose from, but also a decision framework to help you answer critical questions at different stages in your career:
- What skills do I need for my current or next role?
- Which certification will actually help me build those skills?
- How do I avoid learning things I won’t use?
Without a roadmap, most professionals either build skills that don’t align with their role or lack the practical exposure needed to apply them. A structured cybersecurity certification roadmap ensures that every certification you choose directly supports your role, which in turn supports your career growth.
What certifications should beginners start with in cybersecurity?
The Certified Cybersecurity Technician (CCT) is a good option for beginners, helping build multi-domain technical skills with 85+ labs across core cybersecurity domains. The Essentials Series is another option for beginners that offers self-paced video courses covering ethical hacking, network defense, digital forensics, cloud security, IoT security, SOC, threat intelligence, and DevSecOps.
Which cyber certification roadmap is best for career growth?
The EC-Council cyber certification roadmap offers a structured view of career progression in cybersecurity, from no experience to 5 years+. It brings together every stage: foundational (no experience), entry (1–2 years basic knowledge), core (2+ years networking knowledge), specializations, and executive leadership stages (5+ years). This provides clarity on which certifications align with each stage for different roles like security architect, security consultant, application security engineer, and more. It also maps certifications for career paths like blue team, DFIR, security operations, VAPT/pentesting, AI security, and management.
References
Fortinet. (2025). 2025 Cybersecurity Skills Gap Global Research Report. https://www.fortinet.com/content/dam/fortinet/assets/reports/2025-cybersecurity-skills-gap-report.pdf
KPMG. (2025, December). 2025 KPMG Cybersecurity Survey. https://kpmg.com/kpmg-us/content/dam/kpmg/corporate-communications/pdf/KPMG_2025_CybersecuritySurveyReport_Summary%20Slides_Final.pdf
World Economic Forum & Accenture. (2026, January 12). Global Cybersecurity Outlook 2026. https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf