Securing Kubernetes Workloads in the Cloud: Best Practices for Next Gen Business Applications
EC-Council is delighted to present its latest whitepaper titled “Securing Kubernetes Workloads in the Cloud: Best Practices for Next Gen Business Applications,” authored by Dhruva Pudel, Head of Cyber Security, Skillcast Group PLC. This groundbreaking whitepaper delves into the critical challenges of securing Kubernetes workloads in cloud environments. It provides valuable insights and best practices to mitigate risks and safeguard next-generation business applications.
Organizations increasingly rely on cloud-native technologies like Kubernetes to power their business applications in today’s digital landscape. However, securing these workloads in the cloud poses unique challenges that require specialized knowledge and robust security measures. This whitepaper is a comprehensive guide for organizations aiming to fortify their Kubernetes deployments against potential threats and vulnerabilities.
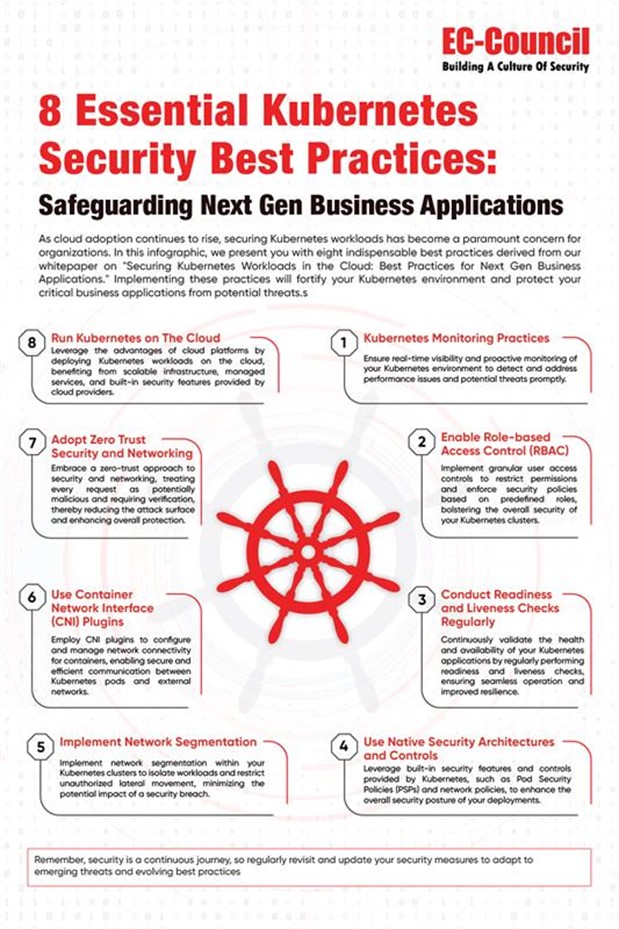
One of the critical insights unveiled in this whitepaper revolves around implementing a defense-in-depth security approach for Kubernetes workloads in the cloud. Recognizing that a single security measure is insufficient to combat sophisticated cyber threats, the whitepaper emphasizes the need for multiple layers of security controls. These include network segmentation, which ensures that workloads are isolated from one another, and authentication and access controls to prevent unauthorized access. Additionally, container security measures are vital to protect individual containers within a Kubernetes cluster. Continuous monitoring of the environment is essential to identify and respond to potential security incidents promptly.
Another crucial insight highlighted in the whitepaper pertains to the significance of regularly updating and patching Kubernetes deployments. As Kubernetes evolves rapidly, new vulnerabilities and security patches are regularly released. Organizations must establish a robust patch management process that ensures the timely application of updates to Kubernetes components, underlying infrastructure, and any associated third-party software. By staying vigilant and proactive in applying patches, organizations can mitigate known vulnerabilities and reduce the risk of exploitation by threat actors.
In conclusion, EC-Council’s whitepaper, “Securing Kubernetes Workloads in the Cloud: Best Practices for Next Gen Business Applications,” authored by Dhruva Pudel, offers invaluable insights and recommendations for organizations aiming to secure their Kubernetes workloads in the cloud. Organizations can strengthen their security posture and protect their next-generation business applications by adopting a defense-in-depth security approach and maintaining regular updates and patching. To access the full whitepaper and embark on the journey towards enhanced Kubernetes workload security, kindly complete the form above and submit your details.