From Reactive to Proactive: How Your SOC Needs to Evolve for Effective Threat Detection and Response
Amid the swiftly changing threat landscape, it has become increasingly crucial for security operations centers (SOCs) to stay proactive. However, many organizations still rely on outdated technologies and processes that are reactive rather than proactive. This is where the concept of next-gen SOC comes into play. In this whitepaper titled “From Reactive to Proactive: How Your SOC Needs to Evolve for Effective Threat Detection and Response,” authored by Pravin Ganesan, readers will learn how to transform their SOC into a proactive defense system using next-generation technologies.
The whitepaper starts by highlighting the challenges faced by SOCs, including the increasing volume and complexity of threats, the shortage of skilled personnel, and the limitations of traditional security tools. It then introduces the concept of a “threat hunting” SOC, which uses proactive techniques to identify potential threats and stop them before they cause any damage. The whitepaper identifies next-gen technologies such as AI-powered threat hunting, deception technology, and advanced analytics as key enablers of this proactive approach.
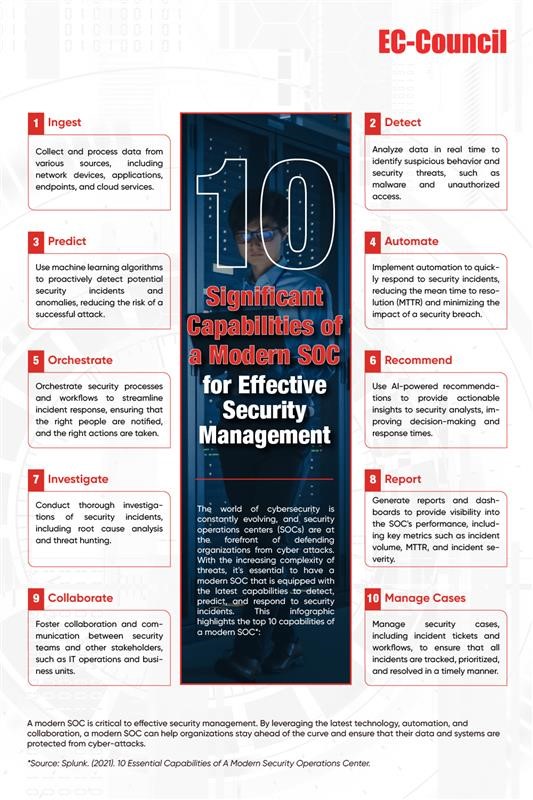
One of the key insights from the whitepaper is the importance of context in threat detection. Traditional security tools often generate a lot of noise and false positives, making it difficult for SOCs to distinguish real threats from benign events. The whitepaper highlights how AI-powered threat-hunting tools can use contextual information such as user behavior, network traffic, and threat intelligence to provide more accurate and meaningful alerts. This helps SOCs focus their attention on the most critical threats and respond to them quickly.
The second key insight delves into the benefits of incorporating threat intelligence into SOC operations. The paper explains how threat intelligence can help SOCs stay ahead of emerging threats by providing real-time information on the latest tactics, techniques, and procedures used by threat actors. The whitepaper also provides examples of how SOCs can incorporate threat intelligence into their operations, such as using it to inform incident response and threat hunting activities.
In conclusion, gain valuable insights into how to implement next-gen SOC technologies, including best practices for deployment, the benefits of automation and orchestration, and the importance of continuous monitoring and analysis. For those seeking to remain knowledgeable about the latest cybersecurity trends and technologies, whether in the role of a security expert or an IT decision-maker, this whitepaper is an indispensable resource. To download the whitepaper and learn more about proactive threat detection, please fill out the form below.