The Certified Ethical Hacker (CEHAI) credentialing created by EC-Council is a respected, trusted and world’s no.1 ethical hacking course in the industry. Since the inception of Certified Ethical Hacker in 2003, the credential has become one of the best options for cybersecurity training across all industries and companies over the world. The CEHAI exam is ANSI 17024 compliant, and teaches AI skill mapped to phases of ethical hacking, adding value and credibility to credential members. It is also listed as a baseline certification in the US Department of Defense (DoD) Directive 8570 and is a NSCS Certified Training.
What Does an Ethical Hacker Do?
An ethical hacker is a cybersecurity professional trained to identify and fix vulnerabilities in systems before malicious hackers can exploit them. They simulate real-world cyberattacks to assess risk and strengthen security posture using multiple techniques, hacking and security tools and ai tools
- Ethical Hackers help organizations answer critical cybersecurity questions:
- What vulnerabilities could an attacker exploit?
- What systems or data are most at risk?
- What damage could an attacker cause with the compromised information?
- How many security layers detect or log the intrusion?
Ethical hackers learn and perform hacking in a professional manner, based on the direction of the client, and later, present a maturity scorecard highlighting their overall risk and vulnerabilities and suggestions to improve.
- What are the best ways to mitigate these vulnerabilities?
They operate under strict authorization, document their findings, and deliver a comprehensive risk and vulnerability scorecard along with actionable recommendations.
Importance of Ethical Hacking?


Jay Bavisi
CEO of EC-CouncilBenefits of Ethical Hacking?
- Discovering vulnerabilities from an attacker’s POV so that weak points can be fixed.
- Implementing a secure network that prevents security breaches.
- Defending national security by protecting data from terrorists.
- Gaining the trust of customers and investors by ensuring the security of their products and data.
- Helping protect networks with real-world assessments.
Practice ethical hacking to Ensure Safe Stay at Home

Types of Ethical Hacking?

Web Application Hacking

System Hacking

Web Server Hacking

Hacking Wireless Network

Social Engineering
Types of Hacking/Hackers
Hackers are of different types and are named based on their intent of the hacking system. Broadly, there are two main types in hacking/hacker – White-Hat hacker and Black-Hat hacker. The names are derived from old Spaghetti Westerns, where the good guy wears a white hat and the bad guy wears a black hat.

White Hat Hacker
Ethical hackers or white hat hackers do not intend to harm the system or organization but they do so, officially, to penetrate and locate the vulnerabilities, providing solutions to fix them and ensure safety.

Black Hat Hacker

Gray Hat Hacker
Core Concepts of System Hacking
Phases of Ethical Hacking
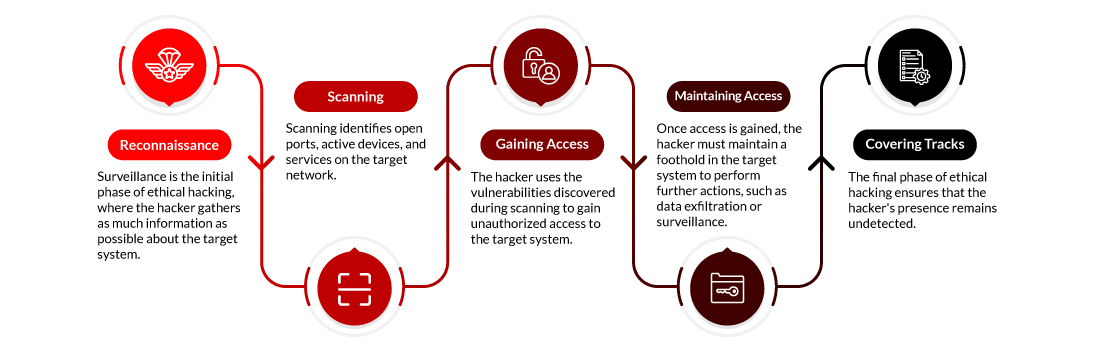
The five phases of ethical hacking are:
1. Reconnaissance
Reconnaissance is the first step in ethical hacking. It’s often referred to as footprinting. Here, a hacker tries collecting various kinds of data, such as employee information, IP addresses, network topology, and domain names, using active and passive approaches. The purpose is to create a diagram of the target’s digital and physical assets.
Active Reconnaissance: This method involves direct interaction with the target system, which may warn the target about possible scans.
Passive Reconnaissance: This implies collecting data without direct contact with the target, making it untraceable.
Popular Tools Used are:
- Nmap
- Whois
- Maltego
Reconnaissance Techniques Commonly Used:
- Google Dorking: Utilizing sophisticated search operators to find sensitive information online.
- Whois Lookup: Collecting information on who owns the domain, IP addresses, etc.
- Social Engineering: Mupulating people into revealing private information regarding targets; this can be done through phishing messages, for instance.
- DNS Enumeration: To create a topology of the target’s infrastructure by finding all DNS entries linked with the domain name concerned.
- Network Scanning: One can learn about active systems and running services using tools like Nmap.
2. Scanning
At that point, the hacker goes to the scanning stage after having enough information. Scanning recognizes open ports, active devices, and services in the targeted network. It also helps to identify areas of vulnerability that can be targeted. Scanning is usually divided into three categories:
- Port Scanning: Finding open ports or services with Nmap or Angry IP Scanner.
- Vulnerability Scanning: Detecting known weaknesses in systems and applications using Nessus.
- Network Mapping: Creating a blueprint of network topology with tools such as SolarWinds.
Popular Tools Used:
- Nessus
- OpenVAS
- Angry IP Scanner
Commonly used techniques for Scanning
- Port Scanning: Using tools like Nmap or Angry IP Scanner to find open ports or services.
- Vulnerability Scanning: Using tools like Nessus to detect known weaknesses in systems and applications.
- Network Mapping: Generating a visual map that shows the network topology with applications like SolarWinds.
- Banner Grabbing: This involves collecting software version information from open services to help determine any weaknesses.
- Ping Sweeps: This entails sending ICMP requests to identify active hosts on a particular network.
3. Gaining Access
During this crucial stage, the intruder utilizes the weaknesses identified during scanning for unauthorized entry into the target system. This may involve leveraging applications, operating systems, or network flaws. The objective is establishing access at different privilege levels, from user accounts to administrative control.
Exploitation Methods comprise buffer overflows, SQL injection, and cross-site scripting (XSS).
Popular Tools Used:
- Metasploit
- SQLmap
- Hydra
Commonly used techniques for Gaining Access:
- Password Cracking: Using brute force and dictionary attacks or to crack passwords, rainbow tables are used.
- Exploration of Vulnerabilities: Unauthorized access can be obtained by exploiting known vulnerabilities such as SQL Injection or buffer overflows.
- Privilege Escalation: Higher-level privileges are acquired within a system through exploitation or misconfiguration.
- Session Hijacking: Taking over a valid session between a user and a system gives entrance without permission.
- Man-in-the-Middle (MITM) Attacks: By intercepting communication between two parties, sensitive data can be accessed, violating confidentiality principles.
4. Maintaining Access
Once inside, the intruder must maintain a presence on the target machine for further actions such as gathering or monitoring sensitive data. Therefore, backdoors, rootkits, or Trojan horses can be installed at this point to ensure continued access to the device even after it has been rebooted or patched.
Persistence Techniques: Employing malicious programs, establishing concealed user accounts, or exploiting cron jobs.
Tools Used:
- Netcat
- Ngrok
- Empire
Standard Methods of Maintaining Access:
- Installing Backdoors: Creating permanent ways of accessing the system later, like backdoors or rootkits.
- Creating Hidden User Accounts: Adding unauthorized users with administrative privileges that are hard to discover.
- Tunneling: Employing strategies such as SSH tunneling for secure communication with an infected machine.
- Keystroke Logging: Capturing user’s keystroke entries to acquire confidential details such as passwords or private information.
- Trojan Horses: Integrating applications that look real but permit unlawful entry.
5. Clearing Track
The finale of ethical hacking revolves around ensuring the hacker remains under the radar. This implies wiping logs, concealing files, and manipulating timestamps to eliminate evidence or proof of any attack. The intention is to ensure that attackers can never be detected or traced via their attack methodology.
Tools Used:
- CCleaner
- Stealth Rootkit
- Timestomp
Standard Methods For Covering Tracks:
- Log Tampering: Deleting or modifying logs to erase evidence of hacking activities.
- Steganography: Hiding malicious files or data within legitimate files to avoid detection.
- File Timestamp Alteration: Changing the timestamps of modified files to mislead investigators.
- Clearing Command Histories: Deleting or altering shell command histories to prevent detection.
- Encryption: Encrypting communication and files to obscure activities makes forensic analysis more difficult.
Master 5 Phases of Ethical Hacking and AI Skills mapped to them with CEHAI
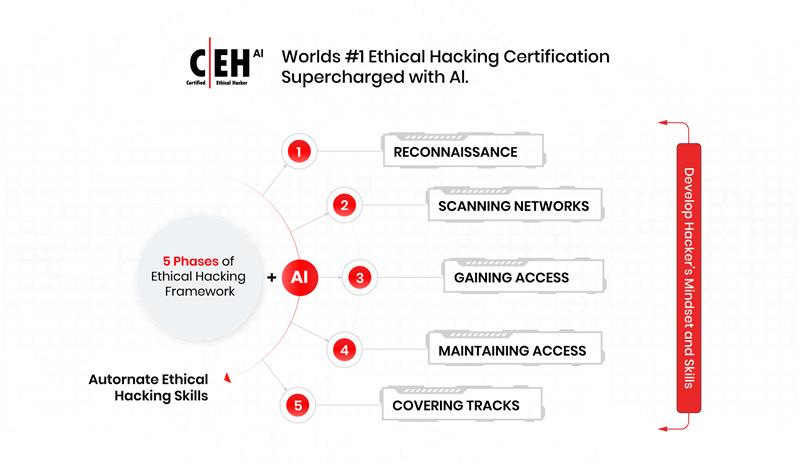
These are the five steps of the CEHAI hacking methodology that ethical hackers or penetration testers can use to detect and identify vulnerabilities, find potential open doors for cyberattacks and mitigate security breaches to secure the organizations. Not just master these 5 phases of ethical hacking but also learn to execute these phases of ethical hacking with AI tools and techniques which enable you to think like an hacker, doubling your hacking skills. To learn more about analyzing and improving security policies, network infrastructure, you can opt for an ethical hacking certification. The Certified Ethical Hacker (CEH v13) designed by EC-Council trains an individual to understand and use hacking tools, AI tools and technologies to hack into an organization legally.
The VAPT (Vulnerability Assessment Penetration Testing) Track includes below 3 Certification at Core:

CND: Certified Network Defender
The Certified Network Defender (CND) certification program focuses on creating network administrators who are trained in protecting, detecting, and responding to threats on a network. The course contains hands-on labs based on major network security tools and techniques which will provide network administrators real-world expertise on current network security technologies and operations. For more details on the CND program, visit the course page.

CEHAI: Certified Ethical Hacker

CEHAI (Practical): Certified Ethical Hacker

Certified Ethical Hacker (Master)
At the advanced level, the VAPT certification track includes three certifications

CTIA: Certified Threat Intelligence Analyst
The Certified Threat Intelligence Analyst (CTIA) program was developed in collaboration with cybersecurity and threat intelligence experts across the globe to help organizations identify and mitigate business risks by converting unknown internal and external threats into known threats. It is a comprehensive, specialist-level program that teaches a structured approach for building effective threat intelligence. Visit the course page to learn more about the CTIA program.
CPENT: Certified Penetration Testing Professional
The program covers advanced windows attacks, how to pen test IoT and OT systems, bypassing filtered networks, how to write your own exploits, single and double pivoting to gain access to hidden networks, master complete pentesting methodology and AI techniques mapped to all pentesting phases, how to conduct advanced privilege escalation as well as binary exploitation.
Through performance-based cyber challenges on live Cyber Range, CPENT Cyber Range provides a hands-on and comprehensive practice based on real-world scenarios to help you gain an edge on penetration tests. The program’s curriculum is designed to help you become a world-class Certified Penetration Tester. If you desire to pursue this program, and ready to take the most difficult cyber challenge, you can visit our Course page to learn more about the CPENT program.

LPT (Master): Licensed Penetration Tester (Master)
The LPT (Master) program is designed to help you join the ranks of elite pen testers through an extensive curriculum based on rigorous real-world penetration testing challenges crafted by industry experts. The program aims to test your penetration testing skills against a multi-layered network architecture with defense-in-depth controls over three intense levels, each with three challenges. The challenges are time-bound; you will need to make informed decisions while choosing your approach and exploits under intense pressure at critical stages.
Suppose you score 90% on the CPENT live range exam. In that case, you will not only earn the CPENT certification, but you will also obtain the prestigious Licensed Penetration Tester (LPT) Master Credential.
Find out what it takes to become the best in penetration testing on LPT (Master) course details page.












