A Guide to Steganography: Meaning, Types, Tools, & Techniques
From invisible ink to highly complex algorithms, this technique is all around us. It is a fascinating and often misunderstood technique of concealing information, and…
Read more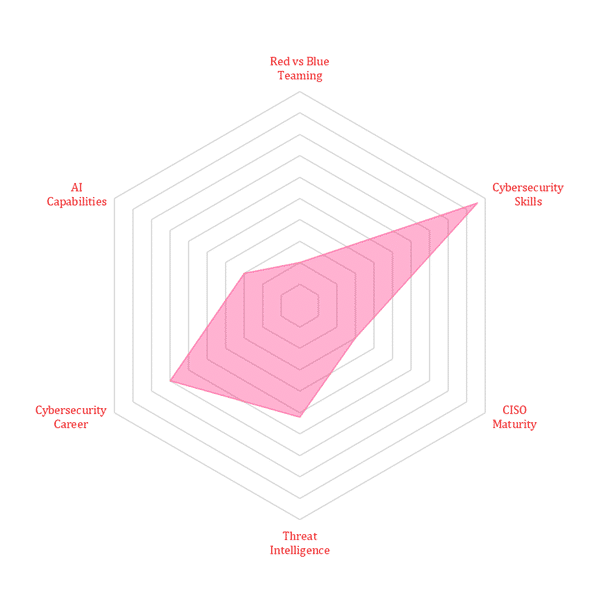
From invisible ink to highly complex algorithms, this technique is all around us. It is a fascinating and often misunderstood technique of concealing information, and…
Read moreSpear phishing is one of the biggest cybersecurity threats that organizations must know. According to Symantec’s Internet Security Threat Report (ISRT), 65% of threat actors…
Read moreModern computing devices generate high volumes of information and are responsible for the retrieval, storage, and processing of information throughout our day-to-day lives. Emerging technologies…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier