Internal and External Network Penetration Testing
Organizations sometimes experience a network penetration incident they could have avoided if their security systems had been strengthened at the time of the attack. These…
Read more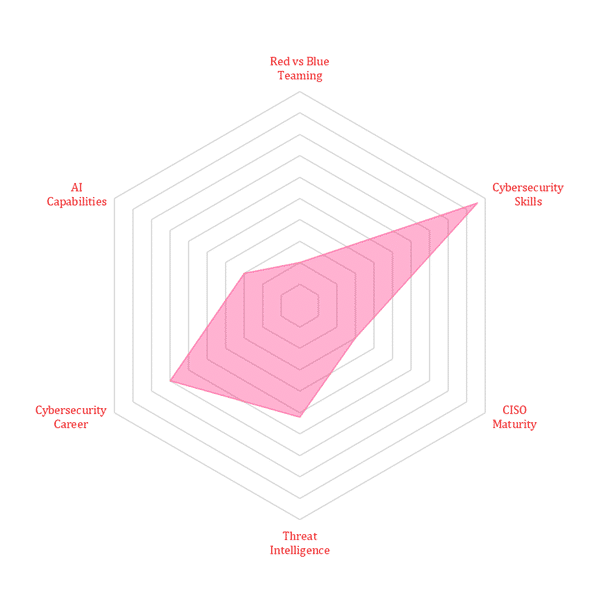
Organizations sometimes experience a network penetration incident they could have avoided if their security systems had been strengthened at the time of the attack. These…
Read moreDate: September 29, 2022Time: 9 a.m. CDT/5 p.m. EAT/7:30 p.m. ISTTopic: Accelerating Your Cybersecurity Career in Today’s IT Ecosystem Watch Now Abstract: Cybersecurity is a…
Read moreCybersecurity is a major focus for businesses now, with companies spending an average of 10.9% of their IT budget on preventing digital threats (Deloitte, 2020). But companies are…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier