Understanding the Skills Needed to Become an Ethical Hacker
As technology advances, so does the need for more robust cybersecurity. Organizations of all sizes are vulnerable to attacks, and to combat these threats, they…
Read more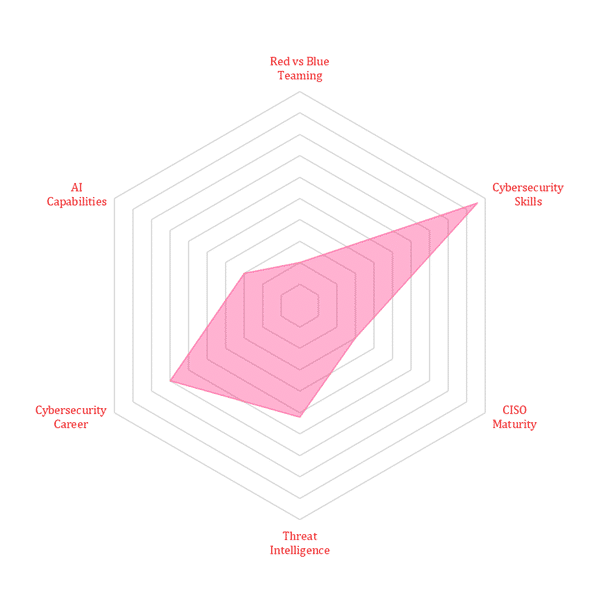
As technology advances, so does the need for more robust cybersecurity. Organizations of all sizes are vulnerable to attacks, and to combat these threats, they…
Read moreMalicious hackers are continually looking for ways to access organizations’ networks and systems to get their hands on valuable company data. In 2020, the FBI…
Read morePenetration testing, also known as pen testing, is a valuable tool that your organization can use to find IT vulnerabilities and secure its network. However,…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier