A Quick Guide to Reverse Engineering Malware
When most people think of malware, they associate it with viruses and Trojans that can cause wreak havoc on their computers. However, malware is a…
Read more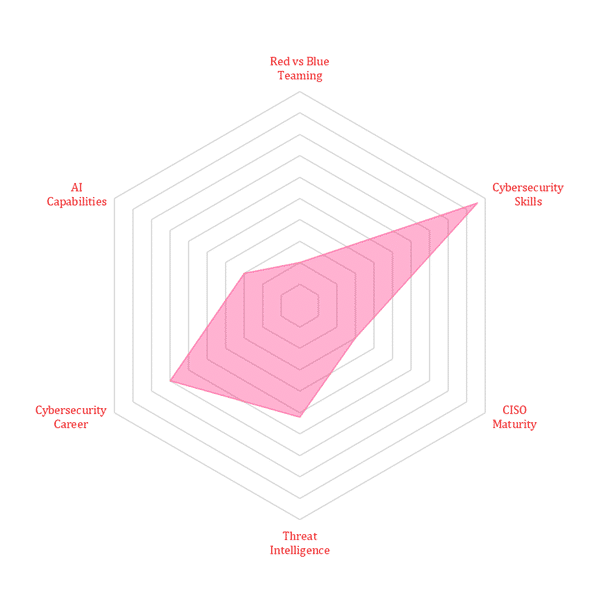
When most people think of malware, they associate it with viruses and Trojans that can cause wreak havoc on their computers. However, malware is a…
Read moreAnyone who operates a computer network is susceptible to security threats and vulnerabilities. Hackers, criminals, and other malicious actors often exploit these weaknesses to steal…
Read moreCloud computing is now an IT best practice for businesses of all sizes and industries. Thanks to the cloud, organizations can use a wide range…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier