Threat Intelligence: The Most Critical Types of Cyberthreats
You already know that there’s no shortage of malicious hackers waiting to get their hands on your most vital personal and business information. With each…
Read more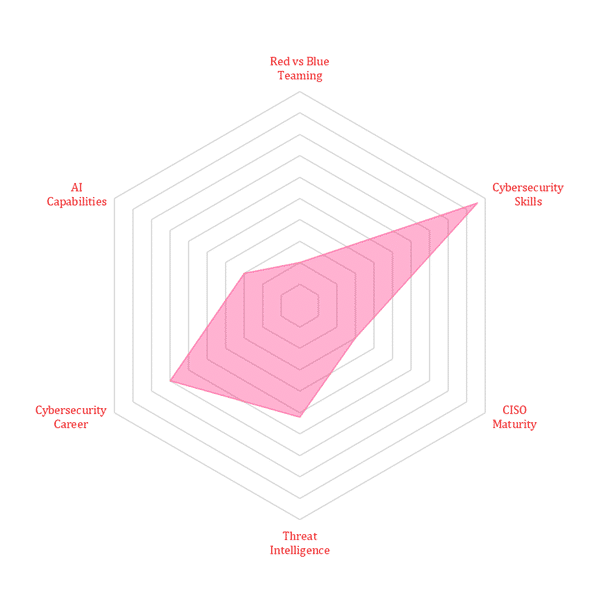
You already know that there’s no shortage of malicious hackers waiting to get their hands on your most vital personal and business information. With each…
Read moreEC-Council is proud to announce the launch of our new cybersecurity technician certification: the Certified Cybersecurity Technician (CCT). This certification, designed for those who want…
Read morePort scanning techniques are a valuable part of any cybersecurity professional’s toolkit. Ethical hackers and penetration testers frequently use port scanning techniques to locate vulnerabilities in a…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier