What is Vulnerability Analysis 101: Everything You Need to Know
Malicious hackers are continually looking for ways to access organizations’ networks and systems to get their hands on valuable company data. In 2020, the FBI…
Read more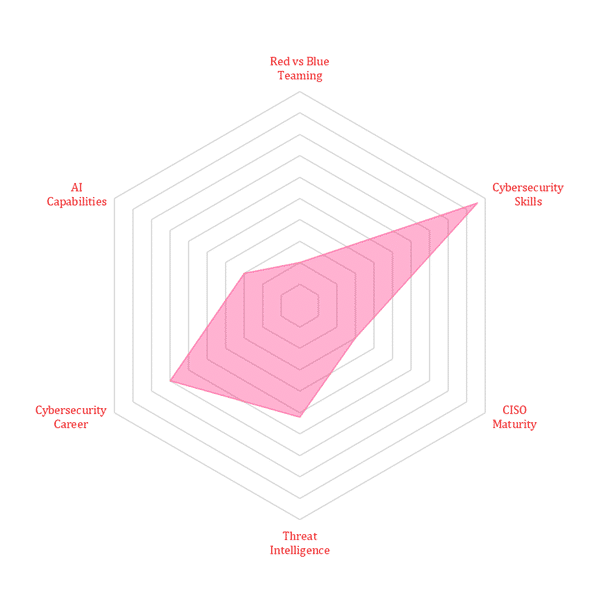
Malicious hackers are continually looking for ways to access organizations’ networks and systems to get their hands on valuable company data. In 2020, the FBI…
Read morePenetration testing, also known as pen testing, is a valuable tool that your organization can use to find IT vulnerabilities and secure its network. However,…
Read moreDate: August 25, 2022Time: 9:30 a.m. CDT/10:30 a.m. EDT/8 p.m. ISTTopic: Protecting the Cloud Computing Environment with CEP Shield against DDoS Attacks Watch NowAbstract: Distributed…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier