An Identity-Based Security Infrastructure for Cloud Environments
To truly comprehend identity-based security, let’s first understand the term “identity.” An identity includes both the login credentials that users use to access IT services…
Read more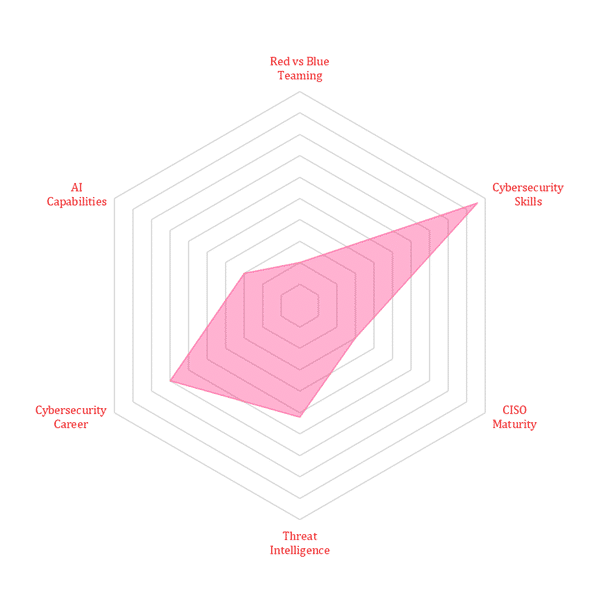
To truly comprehend identity-based security, let’s first understand the term “identity.” An identity includes both the login credentials that users use to access IT services…
Read moreCredential stuffing is a cyberattack technique where attackers use stolen login credentials to gain unauthorized access to user accounts. With the evolving scope of automation…
Read moreDate: June 26, 2024Time: 7:00 PM IST | 8:30 AM CDT | 2:30 PM BST Topic: Exploring the Intersection of Digital Forensics and Identity Management…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier