What does a chief information security officer do, and what are the various CISO roles and responsibilities? As an organization’s most important IT security professional, the CISO is tasked with defending the business from external attackers and cyber threats.
Qualified CISOs must be familiar with many core information security competencies. Below, we’ll look at some essential IT security topics and how CISOs and C|CISO candidates can learn them.
The Fundamentals of Information Security
The IT security field stretches back decades, and organizations have settled on several information security fundamentals and best practices. Just a few of these are:
- Network security: The practice of network security focuses on protecting a company’s network infrastructure from cyber threats such as unauthorized access and data breaches. Solid network security measures include deploying firewalls, IDS/IPS (intrusion detection/prevention systems), secure protocols, and VPNs (virtual private networks). These solutions help safeguard the integrity and confidentiality of information and resources within the organization’s network.
- Encryption: Data encryption is crucial to protect sensitive information in transit and at rest. Effective data encryption relies on converting information into an encoded format using an encryption key; this information can only be decoded and understood with a corresponding decryption key (sometimes the same as the encryption key). Encrypting data ensures that it remains incomprehensible and unusable by anyone except the intended recipient(s), even if it falls into the wrong hands.
- Vulnerability management: It involves proactively identifying, assessing, and mitigating the security vulnerabilities in an IT environment. This requires security assessments, vulnerability scanning, and penetration testing to detect potential weaknesses an attacker can exploit. Organizations can then take preventive actions such as installing patches, software updates, and security solutions.
- Incident response: Organizations must have well-defined and effective plans for responding to security incidents when cyber defenses fail. Incident response involves formulating strategies for events and threats like data breaches or ransomware infections. Effective incident response plans define the roles and responsibilities of IT professionals during a security event and outline the steps to follow to restore normal business operations.
To be effective, CISOs must be familiar with these and other information security fundamentals. These skills and best practices collectively form a solid foundation for IT security, enabling organizations to establish robust defenses against malicious actors. Unfortunately, far too few CISOs measure up to this task: a Gartner study revealed that just 12 percent of CISOs are considered “highly effective.”
Risk Assessment in Information Security
Beyond the fundamental topics listed above, the practice of risk assessment in information security is a crucial component of the CISO job description. The good news is that most CISOs take the risk of cyber attacks seriously. According to a 2023 survey by Proofpoint, 68 percent of CISOs believe their organization is at risk of a cyber attack in the next 12 months, and 25 percent rate this event “very likely.”
The process of risk assessment involves steps such as:
- Identifying assets: The first risk assessment stage involves determining the assets and resources within an organization’s IT infrastructure. These may include hardware, software applications, network devices, data, and intellectual property. By determining the IT assets, CISOs can better prioritize their security efforts and protect the most vulnerable or valuable resources.
- Evaluating threats: The next stage of risk assessment in information security requires CISOs to evaluate the likely threats that their organization faces. Hazards to an IT infrastructure can come from external attackers, insider threats, human error, and natural disasters that can significantly disrupt business operations. CISOs must consider each threat’s nature, capabilities, and likelihood and develop appropriate countermeasures and incident response plans.
- Determining vulnerabilities: Risk assessment involves identifying and mitigating security vulnerabilities and flaws within an IT environment. Malicious actors can find and exploit these weaknesses to launch an attack or extend their reach within the environment. This process involves conducting vulnerability assessments and penetration testing to detect and address weaknesses before attackers discover them.
Conducting risk assessments at regular intervals is a crucial task for CISOs. The cyber security landscape constantly evolves, with new threats and vulnerabilities emerging.
The Operational Aspects of Information Security
Last but not least, the role of CISO—and the function of information security—requires a significant day-to-day operational aspect. The operational components of strong IT security include:
- Security monitoring: Security monitoring involves continuously observing an organization’s IT environment for suspicious events and potential security incidents. This includes monitoring and collecting logs on network traffic, user behavior, and other relevant data sources to identify unusual or unauthorized actions. Security monitoring is often performed by a security operations center (SOC), using tools such as SIEM (security information and event management) to achieve 24/7 visibility into an IT environment
- Incident detection: The goal of monitoring is prompt and accurate incident detection: finding security incidents and events as they occur. IT security professionals use manual and automated incident detection techniques, such as behavioral analytics and machine learning, to identify anomalous patterns and activities. As a result, security analysts can more effectively distinguish normal user activities and traffic from worrisome indicators of compromise (IoCs).
- Incident response: As discussed above, incident response responds to security events identified through incident detection. Incident response involves a series of coordinated, planned actions to contain the incident, mitigate or prevent its impact, remove the threat to the IT environment, and reestablish normal business operations. Effective CISOs create incident response plans for various security events with their IT security teams, including data breaches, malware infections, and denial of service (DoS) attacks.
The operational aspects of information security demand constant vigilance from CISOs. As security threats become more advanced and damaging, CISOs must ensure that security teams are prepared to handle these threats via methods such as training and education programs, simulated attacks and exercises, and penetration testing.
Continuous Professional Development for CISOs and CCISO Candidates
The role of CISO demands a great deal of knowledge of and experience with information security. Moreover, with the cybersecurity landscape continuously shifting, CISOs must stay on their toes to be adequately prepared to address the latest threats and vulnerabilities.
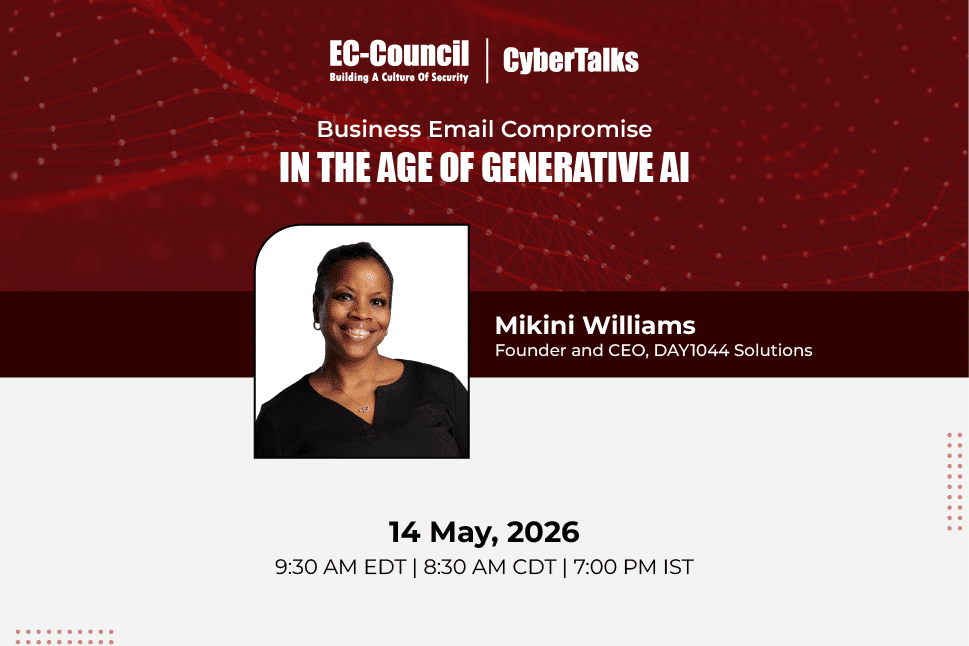
This means that continuous professional development is key for CISOs and aspiring CISOs. Programs such as EC-Council’s Certified Chief Information Security Officer (CCISO) certification offer IT professionals the fundamental skills and training to assume the mantle of CISO effectively.
The CCISO curriculum has been developed by existing CISOs who know what it takes to serve as chief information security officers. CCISO covers the five essential domains of CISO knowledge:
- Governance and risk management
- Information security controls, compliance, and audit management
- Security program management and operations
- Information security core competencies
- Strategic planning, finance, procurement, and vendor management
Ready to assume influential cybersecurity leadership roles? Learn more about the CCISO program today.
References
1. Gartner. (2020). Gartner Survey Reveals Only 12% of CISOs Are Considered “Highly Effective.” https://www.gartner.com/en/newsroom/press-releases/2020-09-17-gartner-survey-reveals-only-12-percent-of-cisos-are-considered-highly-effective
2. Proofpoint. (2023). 2023 Voice of the CISO | Proofpoint US. https://www.proofpoint.com/us/resources/white-papers/voice-of-the-ciso-report
3. Wickramasinghe, Shanika. (2023). Behavioral Analytics Explained: How Analyzing (Odd) Behavior Supports Cybersecurity | Splunk. https://www.splunk.com/en_us/blog/learn/behavioral-analytics.html