Cybersecurity in the Cloud: Threat Eradication, Protection, and Recovery
EC-Council’s whitepaper on Cybersecurity in the Cloud: Threat Eradication, Protection, and Recovery by Satyavathi Divadari, CyberRes Cloud CTO and Head of Enterprise Security Architecture at Micro Focus, provides valuable insights into the threats faced by organizations using cloud-based services and the measures required to protect against them.
The whitepaper highlights the increasing adoption of cloud computing by organizations across the globe, driven by the need for cost savings, scalability, and flexibility. However, this shift towards the cloud has also led to a rise in cyber threats, making it crucial for organizations to ensure the security of their data and applications in the cloud environment.
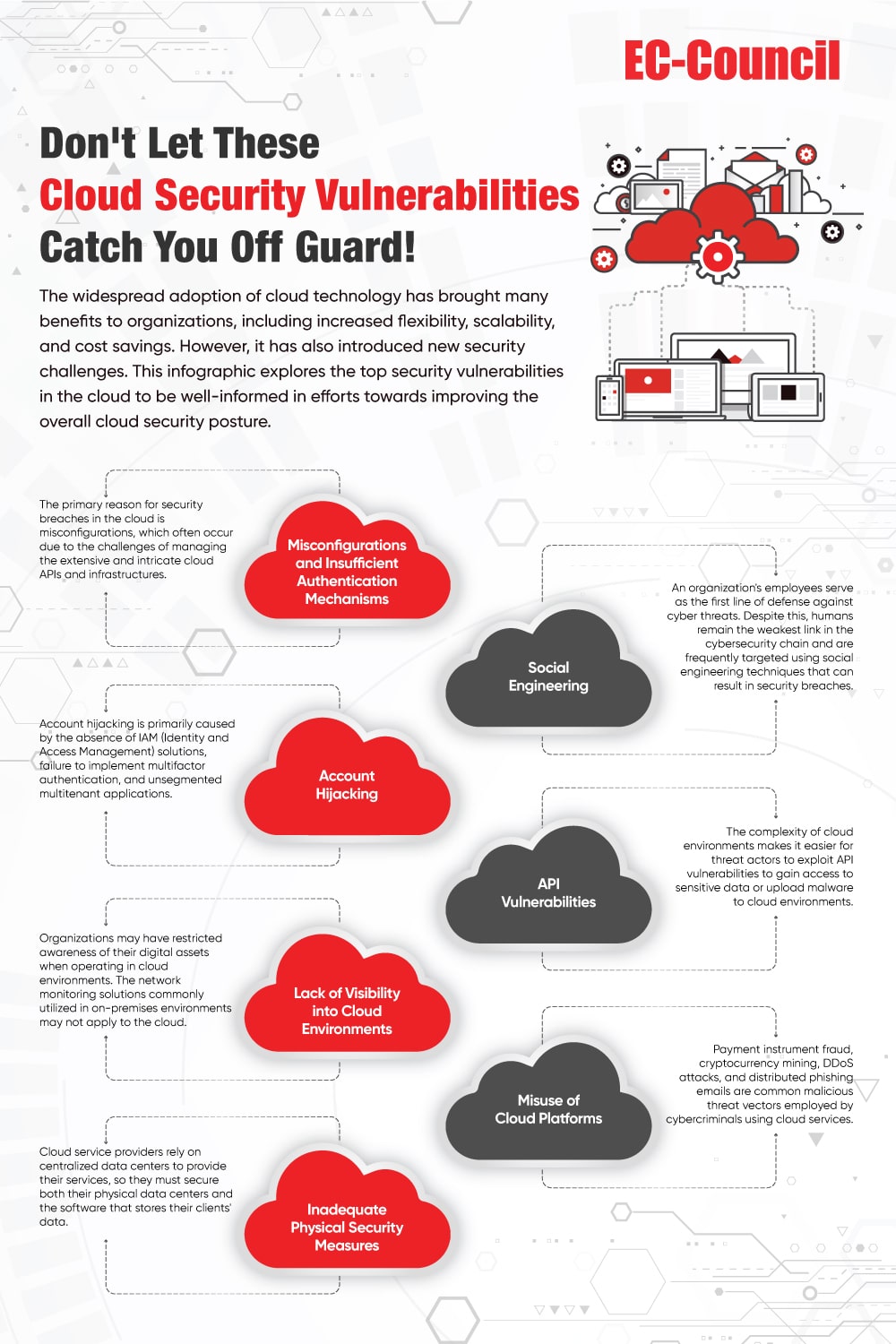
The whitepaper also outlines the key threats organizations face in the cloud, such as data breaches, ransomware attacks, and insider threats. It provides a detailed analysis of these threats and their impact on organizations and offers best practices for mitigating them.
One key insight from the paper is the importance of implementing a comprehensive security strategy encompassing all cloud environment aspects. This includes strong encryption, multi-factor authentication, and regular security audits to ensure the integrity of data and applications. Another critical insight is the need for organizations to have a robust disaster recovery plan to minimize the impact of a cyber-attack or other security incident. The whitepaper also outlines how organizations can develop a successful disaster recovery plan, including identifying critical data and applications, prioritizing recovery efforts, and conducting regular testing to ensure the plan is effective.
In conclusion, EC-Council’s whitepaper on Cybersecurity in the Cloud provides valuable insights into the challenges organizations face in securing their data and applications in the cloud environment. The whitepaper highlights the need for a comprehensive security strategy and a robust disaster recovery plan to minimize the impact of cyber threats. It is an essential reading for any organization looking to adopt cloud computing or enhance its existing cloud security measures.
You can download the whitepaper by submitting your details in the form below to learn more about it. Take the first step towards securing your cloud environment today.