Gaining Access: Unveiling the Techniques, Implications, and Safeguards
Launching a cyber attack on an IT system or network has many similarities with infiltrating a physical building or location. For one, the attackers need…
Read more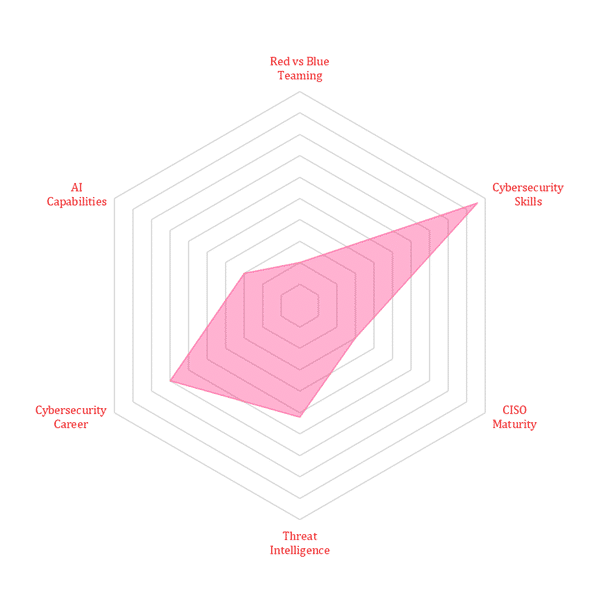
Launching a cyber attack on an IT system or network has many similarities with infiltrating a physical building or location. For one, the attackers need…
Read moreTraditional national security measures of the past leveraged borders, global influence, political maneuvering, and intelligence gathering measures to protect a country’s interests. By shifting focus…
Read moreYou have been in the security industry for a couple of years and are looking for a way to propel your career to the next…
Read moreHome > Cybersecurity Exchange > Cybersecurity Trend Matrix: Securing Tomorrow’s Digital Frontier