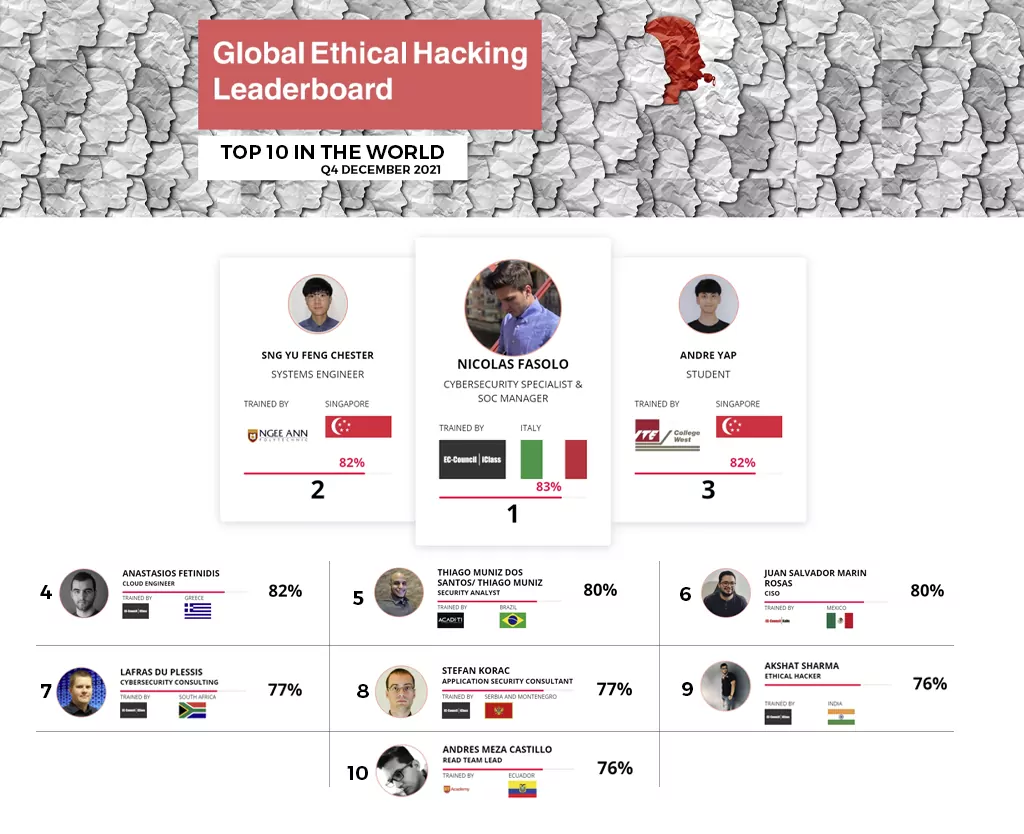
The Cyber Kill Chain: The Seven Steps of a Cyberattack
The Cyber Kill Chain framework, developed by Lockheed Martin (2022), explains how attackers move through networks to identify vulnerabilities that they can then exploit. Attackers use the steps in the Cyber Kill Chain when conducting offensive operations in cyberspace against their targets. If you’re responsible for defending a network, this model can help you understand the stages of a cyberattack and the measures you can take to prevent or intercept each step.
The Cyber Kill Chain is divided into seven stages: reconnaissance, weaponization, delivery, exploitation, installation, command and control (C2), and actions on objectives. This article describes what each of these steps entails, including the preventive measures that network defenders can take in each stage. You’ll also learn how EC-Council’sCertified Threat Intelligence Analyst (C|TIA) certification can advance your cybersecurity knowledge.
1. Reconnaissance
Reconnaissance is the first stage in the Cyber Kill Chain and involves researching potential targets before carrying out any penetration testing. The reconnaissance stage may include identifying potential targets, finding their vulnerabilities, discovering which third parties are connected to them (and what data they can access), and exploring existing entry points as well as finding new ones. Reconnaissance can take place both online and offline.
2. Weaponization
The weaponization stage of the Cyber Kill Chain occurs after reconnaissance has taken place and the attacker has discovered all necessary information about potential targets, such as vulnerabilities. In the weaponization stage, all of the attacker’s preparatory work culminates in the creation of malware to be used against an identified target. Weaponization can include creating new types of malware or modifying existing tools to use in a cyberattack. For example, cybercriminals may make minor modifications to an existing ransomware variant to create a new Cyber Kill Chain tool.
Read article