As more and more of our lives are online, the need for cybersecurity professionals to protect our personal and confidential data from cyberattacks is more important than ever.
Ethical hacking training is an excellent way to get your foot into a fast-paced and lucrative information security career.
Unlike hacking with malicious intent, ethical hacking is done to identify vulnerabilities before they can be exploited. Hacking training gives you the knowledge and skills to assess and secure networks, servers, software, and more. Hacking training courses are the first steps toward your new career if you’re an aspiring ethical hacker.
With the right training, you can proactively protect organizations from the latest cyber threats. Ethical hackers have learned to anticipate how the internet’s bad actors exploit vulnerabilities, thanks to training and experience. Hacking training is the most valuable and practical cybersecurity education available.
Each hacking training program has its focus, but they all have some common objectives and outcomes, such as:
- Penetration testing: Gain hands-on experience by simulating cyberattacks and evaluating the effectiveness of existing security.
- Vulnerability assessment: Learn how to identify security weaknesses in networks, apps, mobile devices, and more.
- Risk management: Prioritize vulnerabilities based on their threat potential and develop mitigation strategies.
- Hacking skills: Hacking training teaches you how systems are exploited and how to use your skills for positive outcomes.
How Does Hacking Training Empower Ethical Hackers?
Hacking training courses empower you to become an ethical hacker by adding to your cybersecurity skill set. You gain technical expertise with a wide array of the top systems used today. By understanding the different types of attack vectors (ransomware, phishing, social engineering, and more), you gain the skills to prevent compromises.
Beyond the tools and techniques, you learn about, hacking training builds up your problem-solving and critical-thinking abilities. Today’s ethical hackers must think creatively and innovatively to stay on top of the ever-evolving threat landscape. The best ethical hacking courses feature exercises that develop analytical thinking.
What Are the Different Types of Hacking Training?
There are several types of hacking training, each with its benefits.
- Certification programs provide comprehensive training while testing and validating the skills you’ve gained. Industry-recognized certifications like Certified Ethical Hacker (CEH) help potential employers recognize your skill levels and capabilities.
- Bootcamps are intensive hacking training programs that pack in a lot of hands-on experience in a short timeframe.
Below are the list of Certification training courses and lot of them relate to cybersecurity. While you understand all the security measures one will not be able to crack or hack any systems. To understand ethical hacking, and conduct penetration testing one needs to get skill from below list of courses, so not just to gather skills and knowledge of a hacker, but also even to think like one.
20+ Hacking Training Courses
Course 1: Certified Ethical Hacker (C|EH)
—The World’s No.1 Ethical Hacking Certification
Program Overview:
EC-Council’s Certified Ethical Hacker Program is a highly sought-after ethical hacking credential and a comprehensive training program designed to create competent ethical hackers equipped with the practical competence necessary to take on various cybersecurity jobs.
Candidates learn core hacking processes and get trained to apply the five phases of hacking: 1. Reconnaissance 2. Scanning 3. Gaining Access 4. Maintaining Access, and 5. Covering Tracks) in identifying security vulnerabilities in target systems.
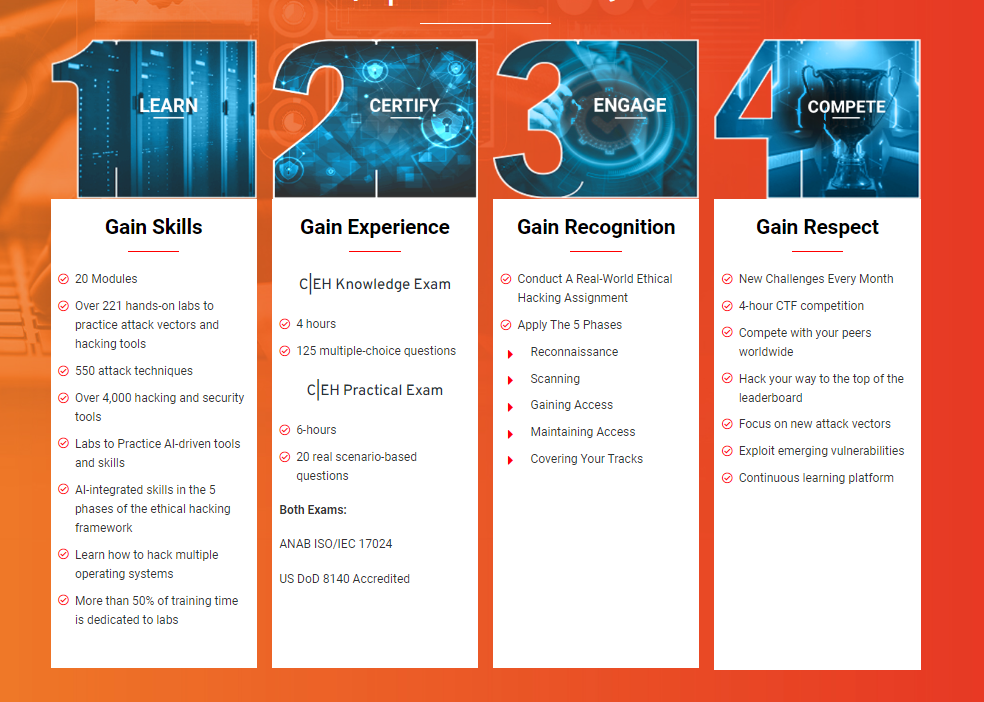
CEH Program is the world’s only cybersecurity training program which incorporates a novel 5 phase learning framework: 1. Learn 2. Certify 3. Engage 4. Compete. This framework was developed to train learners on foundational concepts and expose them to rigorous hands-on practice in a live cyber range environment, enabling them to tackle real-world cybersecurity challenges.




C|EH is trusted by Fortune 500 companies and is relied upon by the Pentagon and by various US government agencies. A golden standard in both public and private sector, the C|EH program used in 7 of the Fortune 10, and 47 of the Fortune 100 across many cybersecurity functions. As per CEH hall of fame report, as survey report done over thousands of cybersecurity professionals; 1 in every 2 professionals received promotions after CEH and 95% of professionals started their career with CEH. Click here to know, DCWF job roles approved under US DoD 8140 for CEH and other EC-Council Certifications.
Proficiency-Level: Beginner to Advanced
- Course Duration: 5days, 40 hours
- Delivery Format: iLearn (Self-Study), iWeek (Live Online), Master Class, Training Partner (In Person)
Assessment: CEH MCQ Exam (4 hours) & CEH Practical Exam (6 hours)
Course Offerings:
The C|EH certification incorporates 20 modules that include the latest technologies, procedures, and methodologies essential to thrive in the current cybersecurity landscape:
Module1: Ethical Hacking
Module 2: Foot Printing and Reconnaissance
Module 3: Scanning Networks
Module 4: Enumeration
Module 5: Vulnerability Analysis
Module 6: System Hacking
Module 7: Malware Threats
Module 8: Sniffing
Module 9: Social Engineering
Module 10: Denial-of-Service
Module 11: Session Hijacking
Module 12: Evading IDS, Firewalls, and Honeypots
Module 13: Hacking Web Servers
Module 14: Hacking Web Applications
Module 15: SQL Injection
Module 16: Hacking Wireless Networks
Module 17: Hacking Mobile Platforms
Module 18: IoT Hacking
Module 19: Cloud Computing
Module 20: Cryptography
The 4 Phase Learning Framework of CEH:
Learn, Certify, Engage and Compete:
Training Format:
Duration: Delivery: iLearn (Self-Study), iWeek (Live Online), Master Class, Training Partner (In Person)
Course Link: https://www.eccouncil.org/train-certify/certified-ethical-hacker-ceh/
Course 2: Ethical Hacking Essentials (EHE)
- Program Overview: EC-Council’s Ethical Hacking Essentials (EHE) is a free, beginner-level cybersecurity training program that helps learners to land entry-level cybersecurity careers. The EHE program trains students in ethical hacking and penetration testing fundamentals and help them acquire practical skills essential to proving their expertise to prospective employers. After successful completion of the course, students will get trained in crucial cybersecurity concepts such as threats and vulnerabilities, password cracking, pen testing fundamentals, cloud computing, and more. While the training is free, the course offers candidates an optional paid upgrade facility to leverage additional facilities like lab activities, EC-Council certification, etc.
- Proficiency-Level: Beginner
- Course Duration: 15 hours
- Delivery Format: 12 premium video lessons
- Assessment: Proctored Exam and Official EC-Council Certification (Available Only with the Ultimate Package)
Certificate of completion: Yes
Course Offerings:
- Information Security Fundamentals
- Ethical Hacking Fundamentals
- Information Security Threats and Vulnerability Assessment
- Password Cracking Techniques and Countermeasures
- Social Engineering Techniques and Countermeasures
- Network Level Attacks and Countermeasures
- Web Application Attacks and Countermeasures
- Wireless Attacks and Countermeasures
- Mobile Attacks and Countermeasures
- IoT and OT Attacks and Countermeasures
- Cloud Computing Threats and Countermeasures
- Penetration Testing Fundamentals
Course Link: https://coderedpro.com/
Course 3: Ethical Hacking for Career Starters
- Program Overview: One of the best ethical hacking courses for beginners, this program introduces candidates to the fundamentals of computer security and networks and offers hands-on learning in the tools and techniques to prevent security breaches.
- Proficiency-Level: Beginner-level
- Course Duration: 4 hours
- Delivery Format: 39 premium video lessons
- Assessment: 7 quizzes and assessments
- Certificate of completion: Yes
Course Outline:
- Introduction to IT and Security
- Attack Types: Part 1
- Attack Types: Part 2
- Securing Passwords and Devices
- Hacking for a good cause
- Hands-on exercises Part 1
- Hands-on exercises Part 2
What will you learn?
- Get equipped with the basics of internet and computer security.
- Learn methods used by hackers use to attack systems.
- Understand the common types of attacks such as denial of service, man in the middle, and phishing attacks and methods used to secure devices.
- Understand how to use Kali Linux in practice and break security controls in practical examples.
Course Link: https://coderedpro.com/products/ethical-hacking-for-career-starters/
Course 4: Recover Lost Data by Hacking Windows
- Program Overview: This course trains learners to recover data in Windows by hacking into the system. Candidates learn to take backup of data, recover deleted data using The Sleuth Kit, learn to use Windows File Recovery App, perform RAID recovery, TAPE recovery and more.
- Proficiency-Level: Beginner
- Course Duration: 6 hours
- Delivery Format: 22 premium video lessons
- Assessment: 6 quizzes and assessments
- Certificate of completion: Yes
Course Outline:
- Introduction to Data Loss Prevention
- Forensic Data Recovery Techniques
- Hard Drive Recovery Tools
- Removable Storage Recovery Process
- Recovering Files from the Cloud
- NTFS, Fat32, and exFAT Data Recovery
- Conclusion and Next Steps
What will you learn?
- The importance of backup as a preventive measure to avoid data loss.
- How to review and analyze data forensic related information?
- How to recover data for directly attached or removable drives?
- Data Recovery Software Tools for NTFS, Fat32 and exFAT data recovery.
Course Link: https://coderedpro.com/products/ethical-hacking-for-career-starters/
Course 5: Wireshark for Ethical Hackers
- Course Overview – Learn Wireshark practically and learn how to analyze and interpret network protocols and leverage Wireshark for what it was originally intended: Deep Packet Inspection and network analysis.
- Course Link – Wireshark for Ethical Hackers | CodeRed (eccouncil.org)
- Course Level – Beginner
- Duration – 6 hours
- No. of Videos – 31
- No. of Assessments – 16
- What You Will Learn –
- A structured approach to database testing and exploitation
- A solid understanding of SQL syntax and operation
- Exploit SQL Injections in Websites and Exfiltrate Data
Course 6: Ethical Hacking with Nmap
- Course Overview – Nmap Tips, Tricks, and Secrets every hacker should know!
- Course Link – Ethical Hacking with Nmap | CodeRed (eccouncil.org)
- Course Level – Beginner
- Duration – 4 hours
- No. of Videos – 43
- No. of Assessments – 30
- What You Will Learn –
- Explore network theory with a pragmatic approach and learn how weaving this knowledge into your Nmap usage can advance your hacking skills!
- Master tuning Nmap for timing and performance, operating system detection, service detection, and version detection.
- Examine advanced enumeration techniques for DNS, HTTP, MySQL, SMB, FTP, SSH, and much more.
Course 7: Getting Started with Vulnerability Analysis and Management
- Course Overview – Practical vulnerability and threat assessment, insight on protecting company.
- Course Link – Getting Started with Vulnerability Analysis and Management (eccouncil.org)
- Course Level – Beginner
- Duration – 5 hours
- No. of Videos – 25
- No. of Assessments – 20
- What You Will Learn –
- Framework to be used for Vulnerability Assessment
- Detect and identify network-based Vulnerabilities
- Automatic and manual method to detect Vulnerability
Course 8: Windows Penetration Testing Essentials
- Course Overview – A Comprehensive Guide to Exploiting the Windows Operating System with Real-world Exploits and Vulnerabilities.
- Course Link – Windows Penetration Testing Essentials | CodeRed (eccouncil.org)
- Course Level – Intermediate
- Duration – 4 hours
- No. of Videos – 25
- No. of Assessments – 15
- What You Will Learn :
- Learn how to set up your own virtual penetration testing lab with active directory and how to obtain evaluation copies of Windows.
- Learn how to perform information gathering and enumeration of Windows-specific services with Nmap and OpenVAS.
- Learn how to identify vulnerabilities like EternalBlue, perform exploitation with Metasploit, and perform system pivoting to establish a foothold on a network.
Course 9: Malware Analysis Fundamentals
- Course Overview – Explore how to find, analyze, and reverse engineer malware.
- Course Link – Malware Analysis Fundamentals | (eccouncil.org)
- Course Level – Beginner
- Duration – 4 hours
- No. of Videos – 26
- No. of Assessments – 30
- What You Will Learn –
- You will learn what virus, worm, Trojan, rootkit, ransomware, mobile malicious code, etc., are.
- Learn how malicious software works and propagates and how they use exploits.
- Learn how to apply your skills to reverse engineer non-malicious software and gain insight into how they operate.
Course 10: Metasploit like a Pro
- Course Overview – Learn to use Metasploit in this beginner-friendly and hands-on course.
- Course Link – Online Course for Penetration Testing with Metasploit |
- Course Level – Intermediate
- Duration – 13 hours
- No. of Videos – 30
- No. of Assessments – 40
- What You Will Learn:
- Understand the basic purpose and use of Metasploit & its history.
- Master techniques used for scanning and enumerating targets.
- Understand how to utilize Metasploit to maintain access and persistence.
Course 11: Mastering Database Reconnaissance and Exploitation
- Course Overview – Learn how to identify, enumerate, and exploit SQL databases and NOSQL databases to PWN modern web applications.
- Course Link – Mastering Database Reconnaissance and Exploitation
- Course Level – Intermediate
- Duration – 4 hours
- No. of Videos – 15
- No. of Assessments – 20
- What You Will Learn:
- After taking this course, you will have an absolute mastery of database exploitation techniques.
- Skills to record findings as you conduct your testing.
- Techniques and methods to help prevent database misconfigurations and common attacks.
Course 12: Getting Started with Kali Linux Penetration Testing
- Course Overview – Learn how to use Kali Linux tools for vulnerability analysis from this hands-on course.
- Course Link – Getting Started with Kali Linux Penetration Testing | CodeRed (eccouncil.org)
- Course Level – Beginner
- Duration – 5 hours
- No. of Videos – 38
- No. of Assessments – 15
- What You Will Learn:
- Learn various Information Gathering tools and techniques.
- Perform Network and Web Vulnerability analysis.
- Learn Database Assessment techniques.
Course 13: Mastering Pentesting using Kali Linux
- Course Overview – Learn Kali Linux tools to become a professional in Penetration Testing.
- Course Link – Master Penetration Testing with Kali Linux Online
- Course Level – Intermediate
- Duration – 5 hours
- No. of Videos – 38
- No. of Assessments – 21
- What You Will Learn :
- Learn Sniffing and Spoofing Tools and Techniques.
- Perform Social Engineering Attacks.
- Learn Forensics Analysis using Forensics Tools.
Course 14: Hands-on Password Attacks and Security
- Course Overview – Learn how attackers can bypass passwords and how you can prevent them from doing so.
- Course Link – Hands-on Password Attacks and Security
- Course Level – Beginner
- Duration – 2 hours
- No. of Videos – 27
- No. of Assessments – 25
- What You Will Learn:
- Prevent brute force attacks, dictionary attacks, rainbow table attacks, and sniffing via keyloggers.
- Bypass passwords using brute force attacks, dictionary attacks, rainbow table attacks, and keyloggers.
- Create strong passwords that you will never forget.
Course 15: Burp Suite: Web Application Penetration Testing
- Course Overview – Simulate attacks through a hands-on approach within your web application with this integrated platform.
- Course Link – Burp Suite: Web Application Penetration Testing
- Course Level – Intermediate
- Duration – 2 hours 46 minutes
- No. of Videos – 21
- No. of Assessments – 15
- What You Will Learn:
- Set up your Burp Suite environment and examine target websites using Burp 2x
- Scan your web application and interpret your results
- Simulate Hybrid Spidering your web application
Course 16: Securing your Network from Attacks
- Course Overview – Learn to identify, mitigate, and prevent network attacks at work or home from this course.
- Course Link – Cybercrime And You: Staying Safe in a Hyper-Connected World
- Course Level – Beginner
- Duration – 6 hours
- No. of Videos – 39
- No. of Assessments – 45
- What You Will Learn:
- How to identify phishing emails, bad links, etc.?
- How to prevent and recover from virus and ransomware attacks?
- Learn how to make your network a harder target.
Course 17: Session Hijacking and Prevention Techniques
- Course Overview – Learn and understand with hands-on experience on various Attack Patterns that are being exploited and to ensure adequate preventive measures are implemented to mitigate these risks
- Course Link – Session Hijacking and Prevention Techniques
- Course Level – Beginner
- Duration – 2 hours
- No. of Videos – 25
- No. of Assessments – 18
- What You Will Learn –
- Learn different vulnerable scenarios such as in Network Protocols, Web Applications, and wireless protocols, and how hackers exploit them.
- Session hijacking (how hackers use it to attack an organization).
- Hands-on experience to use built-in Windows and Linux tools, as well as specialized third-party proxy solutions to detect and exploit vulnerabilities.
Course 18: Power of Next Generation Firewall
- Course Overview – Learn how the main fortress of the network – a Firewall, has evolved so far to protect us against invaders of cyberspace.
- Course Link – Power of Next Generation Firewalls
- Course Level – Advanced
- Duration – 6 hours
- No. of Videos – 45
- No. of Assessments – 40
- What You Will Learn –
- Learn what is a (network) firewall, and why is it useful.?
- Understand how these network firewalls have evolved, and what is a next-generation firewall.?
- Learn how do next-generation firewalls filter the traffic by applications?
Course 19: Intentionally Vulnerable Apps in Action for Ethical Hacking Practice
- Course Overview – Build or sharpen your ethical hacking skills by practicing on intentionally vulnerable apps.
- Course Link – Intentionally-vulnerable Apps in Action for Ethical Hacking Practice
- Course Level – Beginner
- Duration – 4 hours
- No. of Videos – 59
- No. of Assessments – 35
- What You Will Learn –
- Learn what OWASP Top 10 vulnerabilities are practically.
- Find out how SQL Injection attacks are performed.
- Understand Cross-site Scripting attacks including Reflected XSS, DOM XSS, and Stored XSS.
Course 20: The Complete Guide on SQL Injections
- Course Overview – Everything you need to know about attacking SQL injections is laid out step-by-step in this course.
- Course Link – The Complete Guide on SQL Injections
- Course Level – Intermediate
- Duration – 2 hours
- No. of Videos – 10
- No. of Assessments – 35
- What You Will Learn –
- A structured approach to database testing and exploitation.
- Exploit SQL Injections in Websites and Exfiltrate Data.
- A solid understanding of SQL syntax and operation.
Course 21: Ensuring Network Security with Zeek
- Course Overview – Monitor network traffic and detect intrusions using Zeek network analysis tool.
- Course Link – Ensuring Network Security with Zeek
- Course Level – Beginner
- Duration – 4 hours
- No. of Videos – 19
- No. of Assessments – 20
- What You Will Learn –
- You will learn the fundamentals of traditional network segmentation
- You will learn about virtualization technologies
- You will learn the fundamentals of network function virtualization
Course 22: End-to-End Mobile Security
- Course Overview – A comprehensive dive into the world of mobile security.
- Course Link – End-to-End Mobile Security
- Course Level – Beginner
- Duration – 4 hours
- No. of Videos – 23
- No. of Assessments – 25
- What You Will Learn –
- Identifying potential vulnerabilities with your mobile device.
- Security through an MDM.
- Making your connection private.
Course 23: Hands-on IoT Pentesting
- Course Overview – Understanding the Basics of Assembly Language, OS Internals, and Legal Protection Software.
- Course Link – Hands-on IoT Pentesting
- Course Level – Beginner
- Duration – 2 hours
- No. of Videos – 34
- No. of Assessments – 10
- What You Will Learn –
- You will learn about Soldering Basics
- Explore how to analyze Radio Signals
- Learn how to use a Multimeter
Course 24: Introduction to Azure Cloud Security Tools and Services
- Course Overview – Explore the Microsoft Azure Cloud Platform and gain an understanding of the cloud security tools and services that are available.
- Course Link – Introduction to Azure Cloud Security Tools and Services
- Course Level – Beginner
- Duration – 2 hours
- No. of Videos – 14
- No. of Assessments – 14
- What You Will Learn –
- Learn to develop and deploy your applications over Microsoft Azure Cloud Platform.
- Gain command over all the Cloud Security options, services, and tools available with all Identity and Security tools available on AZURE.
- You will get familiarized with Application Gateway and Azure Sentinel.
References
National Defense (2023). Just in: U.S. desperately needs cyber talent, Congress says https://www.nationaldefensemagazine.org/articles/2023/6/26/us-desperately-needs-cyber-talent-congress-says
About the Author
David Tidmarsh is a programmer and writer. He’s worked as a software developer at MIT, has a B.A. in history from Yale, and is currently a graduate student in computer science at UT Austin.