Ready to challenge your skills? Getting ready for a CTF or a Cyber Challenge?
Train With CyberQ Skill Pack Challenges
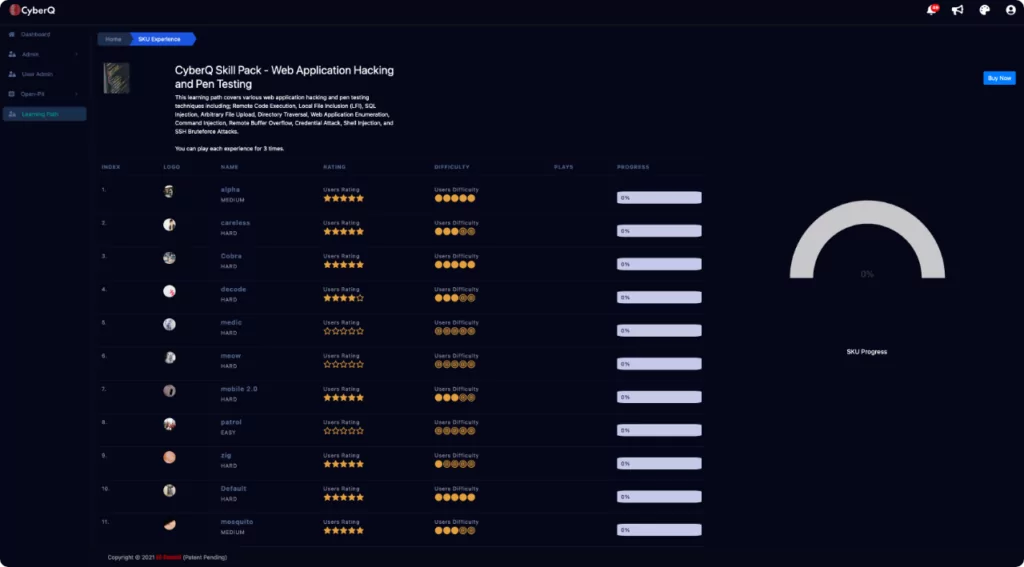
CyberQ Skillpacks are designed to test your skills in a variety of different challenges with limited guidance. Each challenge runs independently as its own “Self-Paced Capture the Flag.” Launching a Skill Pack challenge will reserve your very own space in our CyberQ Data Center, we will raise the Attack Console, as well as the down-range vulnerable targets for you to practice and challenge your skills.

Please note, this is not a learning lab. Skill packs are designed intentionally with challenges, puzzles, and preconfigured targets that will test your ability to identify, analyze, exploit, and own the targets. If you are new to Cyber and have never participated in a cyber challenge or competition, Skill packs may be too advanced. So, feel free to browse our learning products if this describes you, however, if you are ready for a challenge, enjoy solving complex puzzles and testing your limits, CyberQ challenges are a great way to hone your trade craft.
Steganography Techniques Skill Pack
Network Security Engineer Salary
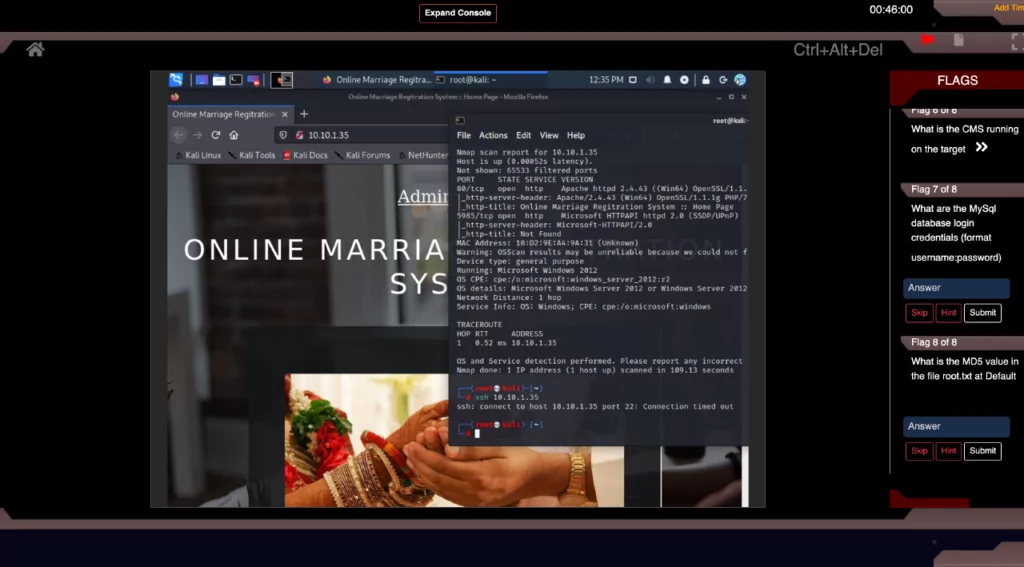
This Skill Pack will challenge your skills in salient web application hacking and penetration testing techniques including; Remote Code Execution, Local File Inclusion (LFI), SQL Injection, Arbitrary File Upload, Directory Traversal, Web Application Enumeration, Command Injection, Remote Buffer Overflow, Credential Attack, Shell Injection, and SSH Bruteforce Attacks.
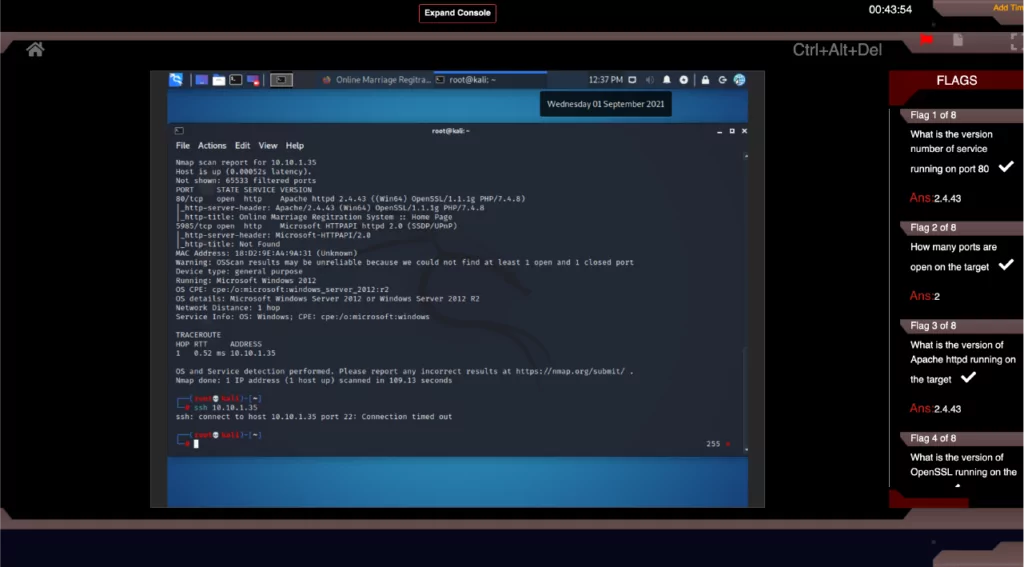
Each challenge contains a fully designed target network with live virtual machines, servers, web hosts, and vulnerable sites and applications. Launching a challenge will open the CyberQ Console and safely connect you to our live attack environment right through your browser. Depending on the challenge, you will land in your attack machine, either Kali or Parrot, where you will have instant access to the full suite of attack tools required to carry out your challenge. Targets are preconfigured with host and application vulnerabilities which you will uncover as you progress through the challenges. CyberQ is a fully automated Cyber Range platform providing you with a self-driven ‘Capture-the-flag‘ experience in each challenge.
Gain direct hands-on practical experience on Industry’s leading Cyber Range Platform – CyberQ. Successful Completion of this Web Application Hacking and Penetration Testing Skill Pack will gain you Job-ready Cyber skills and execution efficiency against cyber challenges.
- Hands-on Experiences with Immersive Scenarios
- Designed for Deep Learning by Cyber Experts
- Latest Threats, Vulnerabilities and Techniques
- Practical Application of Skills on Cutting-edge Cyber Range
- Skills Feedback with Every Exercise
- Fully Loaded Attack Platform
- Preconfigured Live targets and vulnerable Hosts, Sites, and Applications “down-range”
About Steganography Skill Pack
Steganography refers to the art of hiding data “behind” other data without the knowledge of the victim. Thus, steganography hides the existence of a message. It replaces bits of unused data into ordinary files, such as graphics, sound, text, audio, and video with other surreptitious bits. The hidden data can be in the form of plaintext or ciphertext, and sometimes, an image.
Utilizing a graphic image as a cover is the most popular method to conceal the data in files. Unlike encryption, the detection of steganography can be challenging. Thus, steganography techniques are widely used for malicious purposes. For example, attackers can hide a keylogger inside a legitimate image; thus, when the victim clicks on the image, the keylogger captures the victim’s keystrokes. Attackers also use steganography to hide information when encryption is not feasible. In terms of security, it hides the file in an encrypted format, so that even if the attacker decrypts it, the message will remain hidden. Attackers can insert information such as source code for a hacking tool, a list of compromised servers, plans for future attacks, communication and coordination channels, etc.
- Image Steganography: Images are the most popular cover objects used for steganography. In image steganography, the user hides the information in image files of different formats, such as .PNG, .JPG, and .BMP
- Document steganography: In document steganography, the user adds whitespaces and tabs at the ends of the lines.
- OS detection: Nmap detects the Operating system, MAC address, and the software version of the system/target.
- Folder Steganography: Folder steganography refers to hiding one or more files in a folder. In this process, the user moves the file physically but still stays associated to its original folder for recovery.
- Video Steganography: Video steganography is a technique to hide any kind of file with any extension in a carrying video file. One can apply video steganography to different formats of files, such as .AVI, .MPG4, .WMV, etc.
- Audio Steganography: In audio steganography, the user embeds the hidden messages in a digital sound format.
- Whitespace Steganography: In whitespace steganography, the user hides the messages in ASCII text by adding whitespaces to the end of the lines.
- Spam/Email Steganography: One can use spam emails for secret communication by embedding the secret messages in some way and hiding the embedded data in the spam emails. This technique is referred to as spam/email steganography.
Steganography Techniques Covered in the Skill Pack
- Image Steganography
- Web Steganography
Gain related NICE skills for Steganography
S0001
Skill in conducting vulnerability scans and recognizing vulnerabilities in security systems.
S0009
Skill in assessing the robustness of security systems and designs.
S0044
Skill in mimicking threat behaviors.
S0051
Skill in the use of penetration testing tools and techniques.
S0137
Skill in conducting application vulnerability assessments.
S0364
Skill to develop insights about the context of an organization’s threat environment.
Related Job Roles for Steganography
- Blue Team Technician
- Red Team Technician
- Computer Network Defense (CND) Auditor
- Ethical Hacker
- Information Security Engineer
- Internal Enterprise Auditor
- Penetration Tester
- Network Security Engineer
- Technical Surveillance Countermeasures Technician
- Reverse Engineer
- Risk/Vulnerability Analyst
- Vulnerability Manager
Continue on your Cyber Proficiency Journey with Skill Packs Designed by Our Cyber Experts
- Web App Hacking and Pen Testing
- Service Exploitation
- Privilege Escalation
- Red Team Architect
- Cryptography
- Vulnerability Research for Hackers and Pen Testers
- Steganography
- SQL Injection
- Password Cracking